Persona is respected - does NOT send anything to ICE - won't let its software be used for surveillance - and its "leak" was as inconsequential as a "leak" of the HTML code of a web page
Persona IS SAFE. You may see stories claiming that Persona does unauthorised identity searches and updates your data to ICE. This is NONSENSE.
[Skip to Contents]
Video: Persona is respected — does NOT send anything to ICE — and “leak” as inconsequential as HTML “leak”!
Persona’s CEO Rick Song says that that not only don’t they steal the data of clients which would be very illegal. They don’t permit their software to be used by ICE or for surveillance at all.
If you are opposed to how ICE uses data, Persona is one of the best companies to use because of a clear company policy that they will never work for ICE to help it do surveillance.
The stories we’ve had to debunk are completely back to front here.
You may also see false claims that Persona exposed private data on the internet. This is false too. All that happened was a very minor thing.
I have been unable to find any other blog post that explains what a nothingburger it was based on Persona’s own internal review of what happened. But if anyone else wrote about it, it is not going to be shared widely :). A true story saying something that seemed to be scary is a complete nothingburger usually isn’t of much interest on the internet and won’t float up in search results or be shared much.
Their internal review found no security issues. Just an appearance of what seemed to outsiders to be a security incident.
It was a dev server not set up for any client to use, no data on it, and all that was exposed is the JavaScript. Or more technically, a version of JavaScript called Typescript. See:
JavaScript runs in the browser and is visible to a geek just like you can see the HTML code for a web page.
Just as with HTML code, you can’t hide it because the browser needs to download it to run it to show the page to you. You can also set breakpoints on it and step through it in your browser for debugging. And like HTML and unlike the similarly named Java, it’s just plain text directly editable by humans. It’s not even compiled into a more efficient language for computers to use.
Nobody would put anything that needs to be hidden from a hacker in JavaScript.
As Persona puts it in their incident report:
Frontend code is, by definition, public. If you visit withpersona.com/dashboard or go through any Persona verification flow, your browser downloads our entire frontend codebase. You can open your browser’s developer tools right now and inspect it. Source maps make that code easier to read, but they don’t reveal anything that isn’t already there.
Every feature and capability visible in our frontend code is already documented in our Help Center, described in our API documentation, or visible in the customer dashboard. There are no hidden features, no secret endpoints, and no sensitive credentials embedded in our frontend.
https://withpersona.com/blog/post-incident-review-source-map-exposure-non-production-subdomain
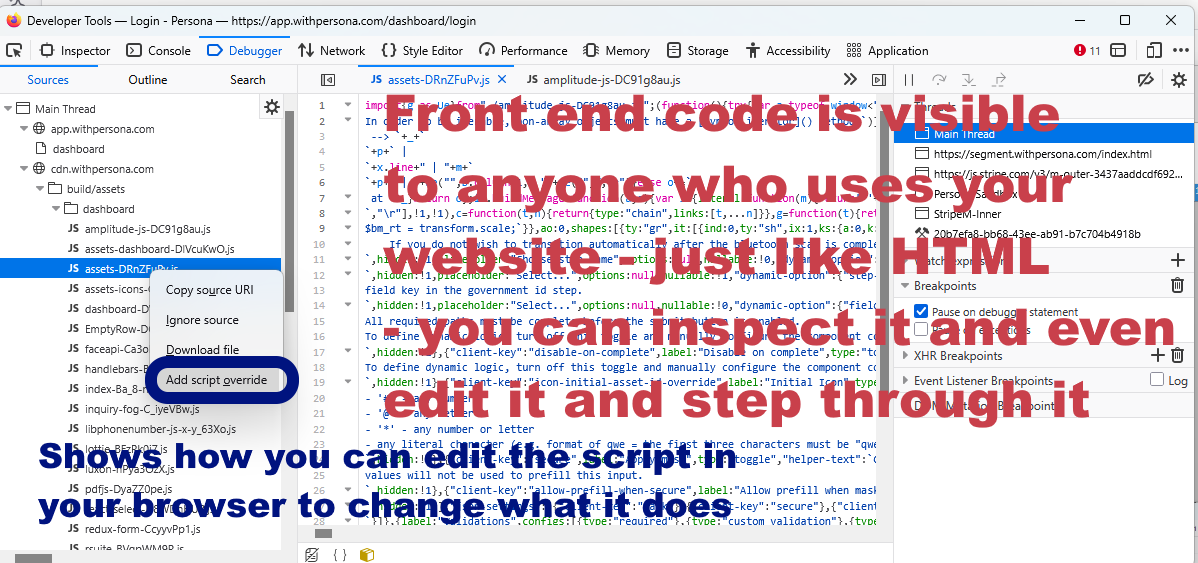
Here I just went to the dashboard url that he provided and looked at some of the front end code in my browser. In Firefox just use F12 and go to the debugger to get here:
TEXT ON GRAPHIC: Front end code is visible to anyone who sees your website - just like HTML - you can inspect it and even edit it and step through it
Shows how you can edit the script in your browser to change what it does
As you can see from the screenshot, if I wanted to, I could make my own file with a copy of their javascript and edit that and change what it does in the browser.
So the back end code is where the security is and the back end code must NOT trust the front end code to even be the code written by the developers.
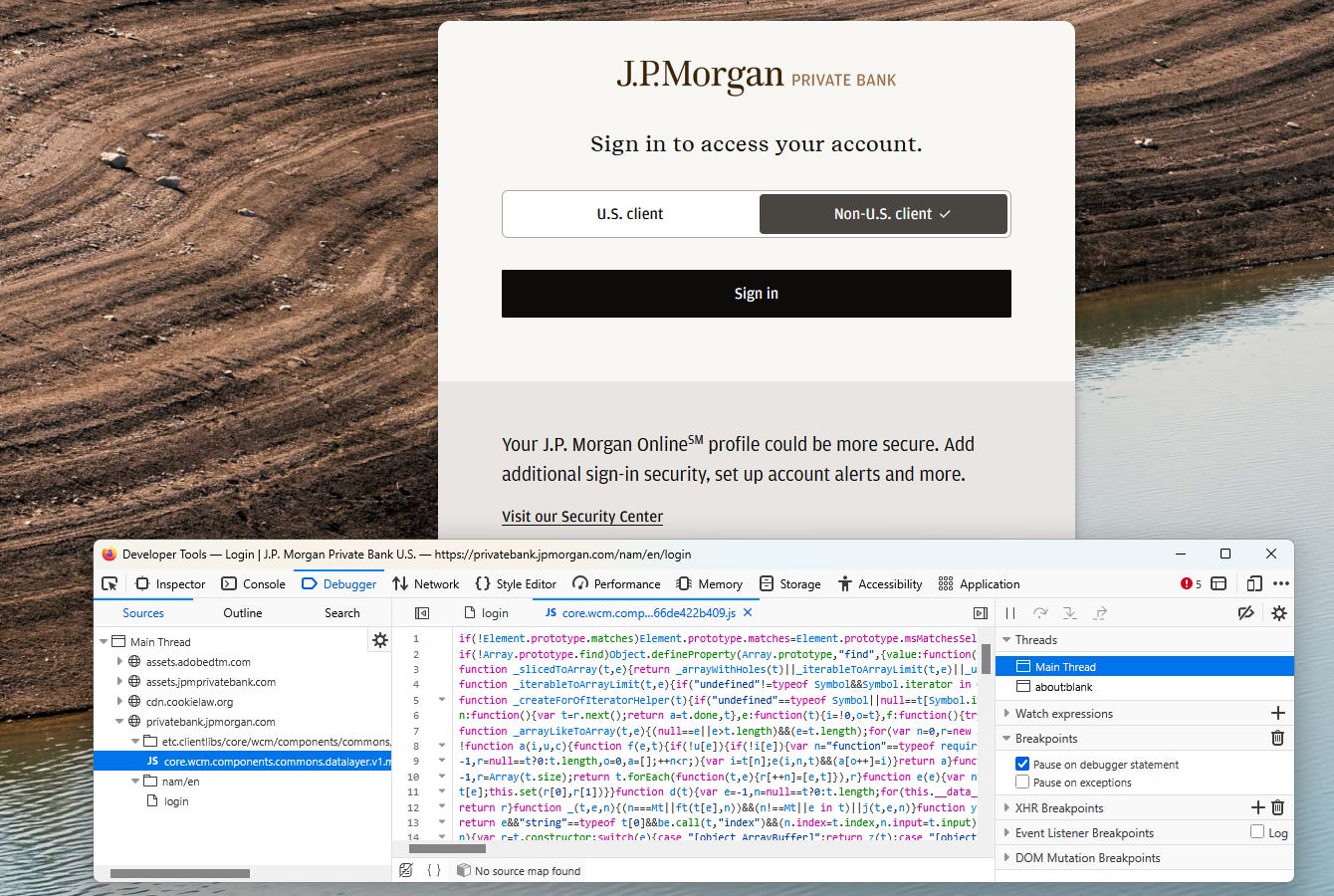
Here for instance is some of the javascript for the login page to a personal account for JP Morgan the largest US bank
https://privatebank.jpmorgan.com/nam/en/login
That is not a security risk. Nobody could hack that code to get into your account because the bank back end won’t trust ANYTHING from the front end. All security screening is done at the back end.
So what did Persona do that all the fuss is about?
Normally it deploys JavaScript to its production web pages as “minified code” which removes all the long names. E.g. a variable called birthDate might be replaced by say “a1” and “selfiePhoto” by “a2”.
On this dev server, it exposed maps that link the abbreviations to the long names.
But
all the long names are documented in Discord’s Application Programming Interface, API that it already has on the internet for the public to read.
See its API guide.
https://docs.withpersona.com/api-introduction
This tells clients how to use Persona, very much like the way the Windows C++ API tells programmers how to use Windows. As an example, as a Windows programmer you can use GetForegroundWindow(); to get whichever window the user is working with. It is not a security issue with Windows to expose the function name GetForegroundWindow.
Similarly a client of Persona can use “birthdate” to retrieve the date of birth found by Persona. For age verification that’s the only thing your program needs. And Persona recommends only asking for the information your program needs:
Using
includeandfieldsto request only the data you need has multiple benefits:
Avoid PII [Personally Identifiable Information] transfer: Some resources, like inquiries, have attributes that contains PII. You can restrict the returned data to avoid fetching PII when you don’t need it.
https://docs.withpersona.com/response-body
You would NEVER put anything of use to a hacker into the front end code. As Persona put it:
Persona’s security architecture is built on a fundamental principle: we do not trust the client [Client code here is a techy term for code running in the browser or on the device - it is Client as opposed to Server]. Our backend systems treat every request from a browser or device as potentially adversarial. Authentication, authorization, data validation, fraud detection signals, and all sensitive logic live server-side. No amount of frontend code inspection changes that.
https://withpersona.com/blog/post-incident-review-source-map-exposure-non-production-subdomain
This is about the terms Client and Server. Client code runs in your browser or on your device, server code runs on the server
https://en.wikipedia.org/wiki/Client_(computing)
And nor should they trust the client code. Anyone can edit the client code in any modern browser to whatever they want it to do.
Also Persona’s CEO Rick Song says that the exposed code
wasn’t production code.
it was early stage dev code.
You’d learn nothing of it of any interest to a hacker from unminified early stage dev code JavaScript!
So why did the developer expose the source maps? It’s because it helps hugely with debugging.
To move quickly during development, the engineer allowed source maps on the subdomain. Source maps are enormously helpful for debugging during active development. The exposure occurred only on this new test “onyx” subdomain, and not on our FedRAMP validated deployment.
https://withpersona.com/blog/post-incident-review-source-map-exposure-non-production-subdomain
He also explains that there was no data on the server.
The internal review turned up no security issues. What it did turn up is an appearance of insecurity. It is important for them to make sure that everything they do is not only secure but couldn’t even appear insecure to someone who doesn’t know how they do things.
When you handle sensitive identity data, as we do, the standard isn't just "is this secure?" It's also "could this appear insecure?" We failed to ask that second question.
https://withpersona.com/blog/post-incident-review-source-map-exposure-non-production-subdomain
They have made a number of changes so that going forward this can’t happen again. For instance they won’t use internal code names like “onyx” in public facing code and they will block the source maps so that only their engineers can see them not external visitors to the website.
I cover what they did to make sure that they don’t get even this appearance of insecurity again at the end of the section:
See also my:
Contents
The main false claim: that Persona steals client’s data and sends it to ICE - not based on ANY admissible evidence
Back to the original claim, the most scary claim. This is the FALSE claim that Persona steals the data of its clients and leaks it to the government, specifically to ICE.
I have already gone into how Persona has no connection with ICE whatsoever. The very convoluted reasoning people give for this is here:
Persona itself says it has NO CONNECTION WITH ICE and don’t want their software to be used by the government for surveillance.
Rick Song CEO of Persona says: “We do not want our technology to be used by ICE or the government or for any surveillance purposes.”
Persona currently has no Federal contacts and publishes them if they do
Here is where he says it: Rick Song’s tweet of the entire correspondence between and Celeste.
That includes Rick Song’s answer to Celeste / vmfunc who did a hatchet job on Persona where he jumped to numerous conclusions without any real evidence for them.
The main supposed “evidence” vmfunc / Celeste gave for a connection between Persona and ICE is that ICE and Persona both used the name “Onyx” in their software.
People who write software have to have names for things and you make up names you find memorable.
Persona says
The name Onyx is named after the Pokemon character Onix / Onyx and nothing to do with the ICE code called Onyx which they didn’t even know about before reading the blog post
This makes sense.
For details of all this see below:
But before I go into all this detail, I will explain why this HAS to be nonsense.
The main false claim that scares people has to be false or else the CEO of Persona, Rick Song, would be in a criminal case by now - a company CAN’T steal data from a client and give it to the government - example of a bank stealing a Monet painting from a bank vault and giving it to the Louvre
It’s a bit like you depositing a Monet painting in a bank safety vault - and then hearing that the bank donated it to the Louvre without asking you.
For a concrete example, this Monet painting probably spent at least some time in a bank vault. It is from the personal collection of the former billionnaire Tony O’Reilly who has completed bankruptcy proceedings in 2024, and had all his wealth confiscated to sell to pay his creditors. He didn’t do anything criminal, he just made a big financial mistake.
https://www.pressreader.com/ireland/irish-daily-mail/20160411/281599534657634
All his assets were sold to pay his creditors.
Suppose that the bank that had that painting in its vaults in 2024 decided to just give it to the Louvre museum in Paris, say.
It couldn’t do that and it would be a scandal, however much some people might think it belongs in the Louvre. Because it didn’t belong to the bank.
It is the same for Persona. A client’s data that they ask Persona to process is just as valuable to the client as a Monet painting is to an art enthusiast, and they depend on Persona to handle it legally.
Persona CAN’T HAND DATA THAT IT IS GIVEN IN CONFIDENCE TO ICE - very illegal. They’d end up in prison and it would be the end of their company.
So this was a VERY SERIOUS FALSE CLAIM that Celeste / Vmfunc made about Persona.
If this really was a true claim, there would have been immediate criminal proceedings against the CEO of Persona, Rick Song.
But this didn’t happen.
All there is from Persona is a single tweet in X that has the exchange of emails between Celeste and Rick Song and a second folow up tweet.
So the claim is clearly false.
I’ve seen many small blogs and tweets repeat the same false claim as if it was proven. Just based on the Celeste / Vmfunc blog post.
They didn’t even check what Rick Song / Persona said in reply.
They essentially said Persona is guilty of a very serious crime, without any evidence except one blog post who said things they couldn’t verify.
As far as I know my blog post is the first one to call out this nonsense and say it’s false.
It’s legal in the US at least to say such things. They have much stronger freedom of speech laws and much weaker defamation laws than in the US. I’m not sure that Celeste / Vmfunc’s blog post would be legal in the UK.
Celeste / Vmfunc who made this false claim was debunked by Persona’s CEO Rick Song in the corresondenes but he /’ she didn’t even publish Rick Song’s responses in the blog post that is so widely shared on social media.
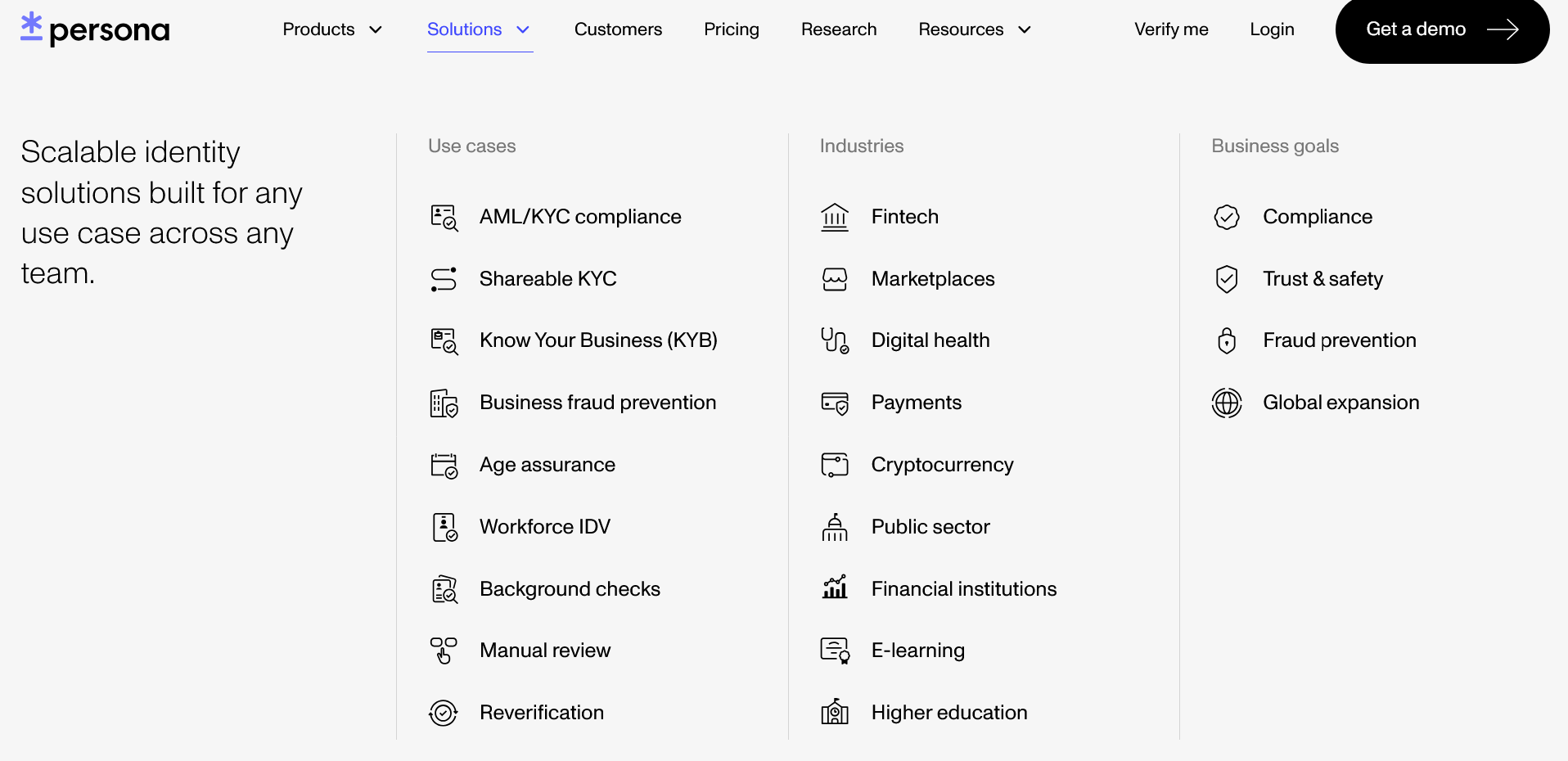
Important to realize these claims are false - because Persona is widely used and trusted and you are likely to come across their name in many places
I am saying this because you may well come across Persona in other contexts. It’s a well-established company that’s been around since 2018.
Here is a complete list of its use cases (a drop down menu)
Use cases
[my expansions of the abbreviations in indented bullets]
AML/KYC compliance
Anti-Money Laundering / Know Your Customer compliance
Shareable KYC
Shareable Know Your Customer (a reusable identity verification process across services)
Know Your Business (KYB)
A due diligence process to verify business entities (similar to KYC but for organizations)
Business fraud prevention
Age assurance
Workforce IDV
Workforce Identity Verification (confirming the identity of employees, contractors, or gig workers)]
Background checks
Manual review
Reverification
Industries
Fintech
Financial Technology (technology-driven financial services)
Marketplaces
Digital health
Payments
Cryptocurrency
Public sector
Financial institutions
E-learning
Higher education
Business goals
Compliance
Trust & safety
Fraud prevention
Global expansion
Click on Solutions here to see the list:
https://withpersona.com/industry/public-sector
Persona is used in the public sector by four states including the largest of them all, California.
California, Ohio, Ontario, West Virginia
https://withpersona.com/industry/public-sector
It is used by employers to verify employees, it’s used in many ways.
For instance if you apply for a job or a bank account your identity may be verified by Persona. Obviously it HAS to check your identity in those cases.
But for age verification all it does is to read the date of birth field on the form and it ignores everything else even your name.
It will
extract only what the client wants it to extract.
Persona is working on software for identity proofing of remote government employees
They had a valid reason for working on software for identity proofing of government employees:
The reason Persona was going through FEDRAMP is because “there has been interest from a couple of agencies to provide identity proofing services for remote federal employees”
That is something Persona can be used for, as a way to prove your identity remotely over the internet.
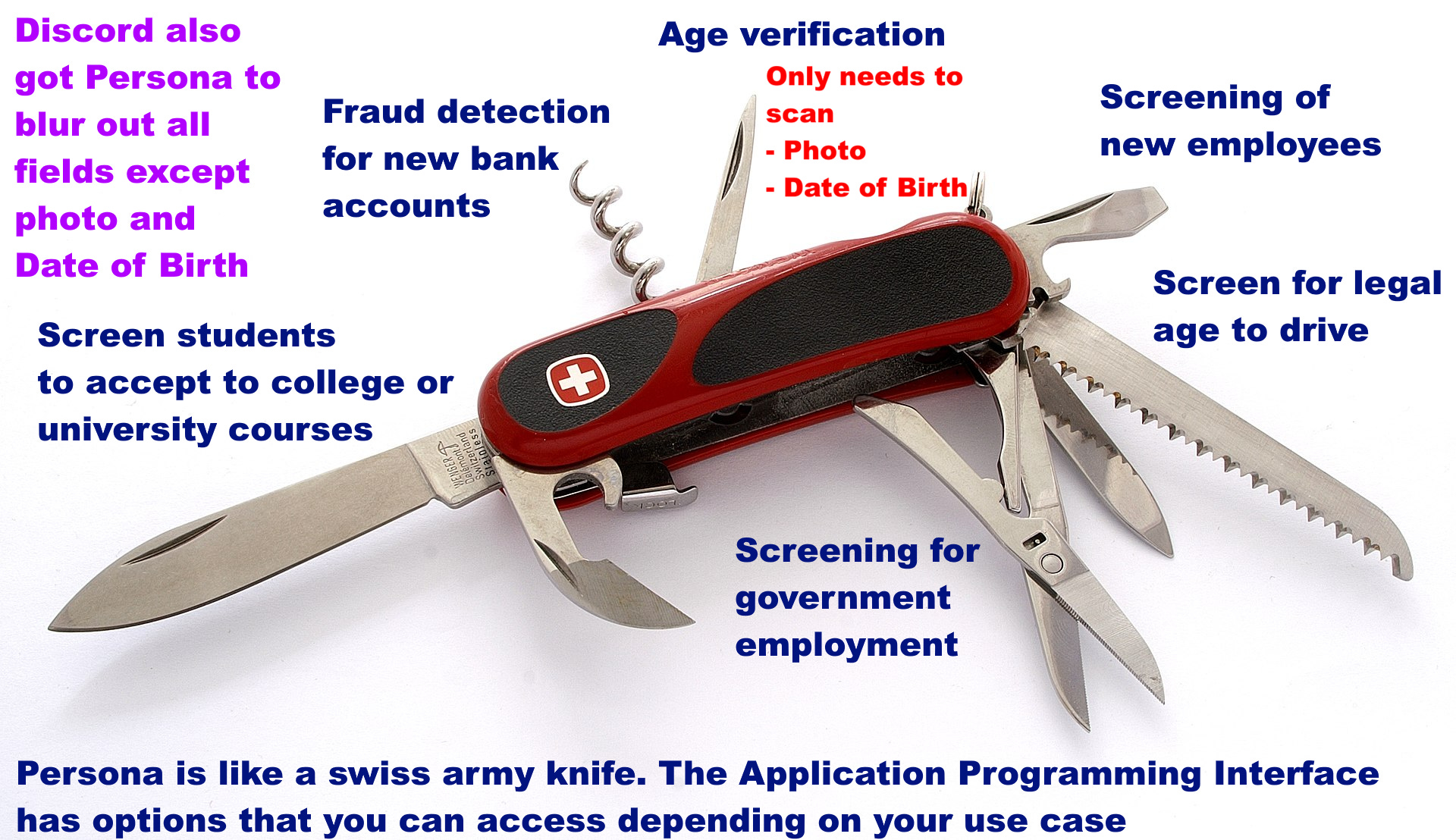
Persona is like a Swiss Knife - multifunction.
Persona is a bit like a swiss army knife.
TEXT ON GRAPHIC
Discord also got Persona to blur out all fields except photo and Date of Birth
Fraud detection for new bank accounts
Age verification
Only needs to scan
Photo
Date of Birth
Screening of new employees
Screen for legal age to drive
Screen students to accept to college or university courses
Screening for government employment
Persona is like a swiss army knife. The Application Programming Interface has options that you can access depending on your use case
Graphic from: https://commons.wikimedia.org/wiki/File:Wenger_EvoGrip_S17.JPG
When used for age verification it does NOT DO IDENTITY PROOFING.
Persona will only do identity checks if that is what a client wants the software to do.
For age verification the client will typically only ask Persona to produce a pass / fail on whether the user is adult. It will typically also require Persona to delete all the data very fast, immediately or in 7 days.
For fraud detection and identity proofing then Persona is even legally required to do much more than that.
But all the data kept secret and then follow whatever the laws are about whether / what has to be retained to comply with the legal requirements to prevent fraud e.g. to vet a new bank customer, or to vet a government employer etc.
Persona will only do what the client asks them to do
The very inconsequential Persona leak - only code that is already as visible to hackers as the HTML in a web page
Short summary of what I found out about the leak.
Persona did have a leak
But this was a very minor leak that doesn’t affect customers in any way
The code that got leaked is
NOT active, not in use by any client and the devs weren’t even working on it
code in development different from the working code used by clients
NOT populated with any real data
code that has to be public anyway because of the way web pages work
Technically what it used was javascript. This runs in the web browser and can’t be hidden because anyone who looks under the hood sees it. All the modern browsers let you see all the javascript any web page uses and even edit it to change the appearance of the page.
However often the javascript is “minimized” so it uses as few bytes as possible transferred to your computer. The main way to do that is to replace long descriptive names of functions and fields with short random text.
E.g. birthDate might be replaced by a1 say
and selfiePhoto by a2 and so on.
Sometimes the code is also obfuscated - this means moving lines of code around and making the program hop around in strange ways so it does exactly the same things but is harder for a human to read. They didn’t say that they do this to the code.
You don’t really have to obfuscate javascript because you expect a hacker to be able to see it and modify it,. step through it and be able to figure out what it is doing. It is the back end that the hacker can’t see that needs to be secure not the javascript which can never be very secure and so is designed so it doesn’t have to be.
Because the code has to be public anyway and visible in web pages the CEO of Persona says the main thing that got leaked was
Names of functions and variables - which are already published in the Application Programming Interface for Persona clients
They do use obfuscation techniques, but just as one layer. They don’t rely on them.
We do employ obfuscation techniques in our frontend code to increase the cost and difficulty of reverse-engineering our fraud detection signals. These techniques are one layer in a defense-in-depth strategy. They raise the bar, but we don’t rely on them as a primary security control. There is active internal and external debate about the efficacy of frontend obfuscation: if someone is sophisticated enough to reverse-engineer minified JavaScript to bypass detection, having access to source maps is unlikely to be the bottleneck.
Persona says that they even included the source maps in earlier versions of Persona. They removed them and used obfuscation techniques just to make casual reverse-engineering less convenient.
In fact, Persona historically shipped with source maps enabled in production. We moved away from that as part of a broader effort to make casual reverse-engineering less convenient, not because we considered exposed source maps a security vulnerability.
https://withpersona.com/blog/post-incident-review-source-map-exposure-non-production-subdomain
There is no sensitive data in their frontend code
There is no sensitive data in our frontend code. No API keys, no secrets, no credentials, no customer data. This is by design.
https://withpersona.com/blog/post-incident-review-source-map-exposure-non-production-subdomain
As I said in the intro, repeating what I said, the internal review turned up no security issues. What it did turn up is an appearance of insecurity. It is important for them to make sure that everything they do is not only secure but couldn’t even appear insecure to someone who doesn’t know how they do things.
When you handle sensitive identity data, as we do, the standard isn’t just “is this secure?” It’s also “could this appear insecure?” We failed to ask that second question.
https://withpersona.com/blog/post-incident-review-source-map-exposure-non-production-subdomain
They have made a number of changes so that going forward this can’t happen again. For instance they won’t use internal code names like “onyx” in public facing code and they will block the source maps so that only their engineers can see them not external visitors to the website.
We are implementing the following changes to strengthen our security controls and compliance practices across all environments:
Establishing a clear source map policy. We now have an explicit, unambiguous policy: source maps must not be publicly accessible on any environment, production or otherwise.
Automated source map blocking. We are deploying WAF rules that automatically strip or reject requests for source map files. Even if a build were to inadvertently include source maps, they would never be served to an external requester.
Hardening non-production environments. We are implementing infrastructure-level guardrails on non-production environments to enforce consistent security baselines, regardless of whether those environments contain data.
Eliminating public-facing codenames. Going forward, all publicly resolvable subdomains and endpoints will use clear, descriptive names. Internal project codenames will remain internal.
Reviewing through a perception lens. We are adding a step to our security review process that explicitly evaluates not just “is this secure?” but “could this appear insecure to a reasonable external observer?” Persona handles sensitive identity verification data. We owe it to our customers and their end users to hold ourselves to a standard that accounts for perception, not just technical risk.
https://withpersona.com/blog/post-incident-review-source-map-exposure-non-production-subdomain
So this whole thing is a nothingburger
It isn’t even a security incident at all. Just an appearance of a security incident to the uninformed.
This is the first blog post to report what Rick Song said back to Celeste that I can find
I have not yet found ANYONE who has read what Rick Song said back to Celeste and published what he said.
They ALL just present Celeste’s side of the story which doesn’t even mention Rick Song’s debunks of what Celeste said to Song.
However there are mitigating circumstances that turn this from a serious breach to a minor lapse. Mainly
it was dev code on a dev server that isn’t connected to any client or data and at an early stage of development
A dev shouldn’t do that but it’s not a serious lapse in terms of customer security
It is front end javascript which means you can inspect the code in your browser anyway - you do get more information from the dump such as names of features but those are already in the API publicly disclosed
Onyx is named after the Onix / Onyx Pokemon character nothing to do with ICE and Persona didn’t know that ICE used the same name for some of their code.
Rick Song said: “We do not want our technology to be used by ICE or the government or for any surveillance purposes.”
Persona doesn’t currently have any government contracts though it is preparing for two possible contracts for identity proofing for remote workers.
The main thing is there is nothing here to be scared of, nobody did anything bad. It was a minor mistake / lapse. Since the code was early dev and not connected to any data or client - that’s why they didn’t need to alert customers to what happened and why Persona handled it just by sharing the correspondence publicly on X.
Many other details, here is my deep dive.
It was early stage dev code on a dev server not in use at the time and not connected to any clients or data
However, what vmfunc didn’t correct the article to explain is that
it was early stage dev code on a dev server
the dev server wasn’t even in use at the time of the breach
not connected to any clients or data
not been through security review (so wouldn’t tell a hacker much about how they make their code secure from hacking)
These details turn it from a serious failing to a minor issue that doesn’t impact on customers. The devs shouldn’t have done this, but it doesn’t have any serious security issues.
That is why Persona treated it as a minor incident just needing a public response on X. Because it is.
It is a mistake, a somewhat embarrassing mistake for such a reputable company - but not one with any risk to customers.
In principle it might be of some very limited use to a hacker but clearly not enough use to do more than tweet to his X account the corespondence with vmfunc.
It was front end javascript - the main thing leaked were the names of the features but these are set out in the API anyway
Rick Song later tweeted:
Persona was not hacked. No database was breached. Frontend code source maps were leaked, which means unminified variable names were exposed revealing all the names of our features. These names are already publicly listed in @Persona_IDV’s help center and API documentation.
To explain what he means here by minified code.
Minifying means replacing the descriptive names with random short variable names to reduce the amount of code to download onto your browser first time you connect to it.
Often it is obfuscated as well as minified. That means you can move bits of code around and do various other things to make it very difficult for a human to read with no change in how the code works.
But
it is front end javascript - this means that when it is in use, the user can inspect it in their browser, step through it, see what it does and so on.
All you can do to obscure it is to minify it or move code around to make it harder to read. The user can show all the javascript with “inspect element” or similar in your browser. It’s not really possible to hide what it does, just make it a bit harder for a hacker to understand.
Technically what was exposed is Typescript. It adds capabilities to catch errors early on to Javascript
https://www.typescriptlang.org/
The real security layer is in the back-end code that a hacker can’t see or access. You would NEVER put anything that needs to be hidden from a hacker in javascript. If it is javascript a determined hacker will be able to figure out a lot about how it works in one way or another.
Persona’s policy is that they do not want their technology to be used by ICE or for government surveillance - they have no current federal contracts but two potential future federal contracts for identity proofing for remote employees
Also on ICE, Rick Song told Celeste (vmfunc):
Persona currently has no Federal contacts and publishes them if they do
“We do not want our technology to be used by ICE or the government or for any surveillance purposes.”
The reason Persona was going through FEDRAMP is because “there has been interest from a couple of agencies to provide identity proofing services for remote federal employees”
Rick Song asked Celeste to remove names of engineers because they are being harrassed because of Celeste’s FALSE claims
Then he asks Celeste to remove the names in his blog post of individual engineers and replace them with himself and other leaders of Persona because they are getting threats and harrassment because of Celeste’s FALSE claims of a connection with Palantir / ICE.
… the implied tie between Palantir/ICE/Persona/betrayal from your post is leading to a lot of fear/anxiety and direct/violent threats to them [Employees of Persona listed in the blog post] particularly accusing them for something that we do not do/have never been involved in (we have no relationship whatsoever with ICE, Palantir, and the other vendors listed).
Some of the folks listed are new grads/interns/people who haven’t been at Persona for a long time, and they shouldn’t have this burden placed on them. I don’t think these people are the ones that the public’s ire should be directed at, and if anyone, it should be directed at me.
In his final email Rick Song asks Celeste to replace these names by himself and four others at his company with their Linkedn profiles.
Celeste just removed the engineers’ names and didn’t replace them with Rick Song etc, writing in his blog:
this used to host a list of people who have worked on this, but since the internet can’t behave after 46 years and feels the need to perform some vigilante justice against people they dont know at all—when the intended audience was family members and friends, you can enjoy finding that info yourself now
He hasn’t updated it with any of the other information from his correspondence with Rick Song, such as that Onyx refers to a pokemon character or that it was a dev server or Rick Song’s statement that “We do not want our technology to be used by ICE or the government or for any surveillance purposes.”.
Highlights of Rick Song’s emails to Celeste (vmfunc)
‘withpersona-gov.com’ is currently under development and is not actively used right now. For context, we’re currently working through the FedRAMP process since there has been interest from a couple of agencies to provide identity proofing services for remote federal employees. We do not want our technology to be used by ICE or the government or for any surveillance purposes.
Unfortunately, providing the sourcemaps was an oversight by the team working on this, and we haven’t started an in-depth security review / pen test on the project yet given it’s still in early development.
[This just means they do in-depth security reviews of all their code but this is still in early development and not got to the security review stage yet]
…
To provide some additional context here, the cluster you found is one we are actively migrating to and under development.
[It is a website they are in the process of migrating to]
This cluster is not the same one that was evaluated for FedRAMP (which does not have the source maps visible).
[It is not the one evaluated for the government to use]
This new cluster is under development to provide better reliability/redundancy which was feedback from our original assessment. However, to reiterate, you are 100% right that it is never good to have unminified typescript+source maps served to the public web and it is a miss on our end.
…
Furthermore, all federal contracts are public and you can confirm that we have no federal contracts today. Transparently, we are actively working on a couple of potential contracts (hence FedRAMP), but these are entirely for the purpose of employee account security and you will be able to see these engagements publicly listed if we happen to move forward.
…
I know that all of the information you’ve shared on these individuals is public and on their social profiles, and I also know that there’s no malice in your listing of them. However, the implied tie between Palantir/ICE/Persona/betrayal from your post is leading to a lot of fear/anxiety and direct/violent threats to them particularly accusing them for something that we do not do/have never been involved in (we have no relationship whatsoever with ICE, Palantir, and the other vendors listed).
Some of the folks listed are new grads/interns/people who haven’t been at Persona for a long time, and they shouldn’t have this burden placed on them. I don’t think these people are the ones that the public’s ire should be directed at, and if anyone, it should be directed at me.
…
For example, the Onyx name has no association with ICE (we weren’t even aware until your blog post!) – it’s actually named after a coworker’s favorite Pokemon.
Here the Pokemon character is meant to be spelt “Onix” but in one release it was accidentally spelt Onyx and ever since then many people think of it as Onyx like the precious stone.
Reddit uses Persona. This is a reputable age verification company and all it extracts from the photo ID is your date of birth and the photo. It then matches the photo with the birth date Then it deletes everything retaining only a pass or fail for adult and birth date. It never gets any information about your reddit activity.
So it is credible that it was named after a favorite Pokemon
Complete correspondence between Celeste and Rick Song
Here is the complete correspondence. It is from this tweet:
Rick Song’s third email, Feb 17, 2026, 8:58 PM
Rick Song [rick@withpersona.com](mailto:rick@withpersona.com)
to celeste ▼Just to be proactive in the interest of removing the referenced individuals sooner + operating in good faith, here is a quick list of executives/leaders and their LinkedIns that can be listed.
Rick Song - linkedin.com
Charles Yeh - Charles Yeh - Persona | LinkedIn
Christie Kim - https://www.linkedin.com/in/christiekmck/
Duncan Sharp - Duncan Sharp - United States | Professional Profile | LinkedIn
Neal Harris - Neal Harris - Neal Harris Investments | LinkedIn
I’ve already reached out to all of the above folks notifying them of my intent to send this note and received their consent. I can also provide more names if needed.
…
—
Rick Song’s second email, Feb 17, 2026, 4:41 PM
I have indented the comments from Celeste that he responds to:
Rick Song [rick@withpersona.com](mailto:rick@withpersona.com)
to celeste ▼Thank you for responding – and genuinely appreciate how you are engaging on this.
| answer the 18 questions in writing. take your time. i’m not trying to rush you into something sloppy. be as detailed or as high-level as you’re comfortable with. if there are things you genuinely can’t answer for legal or competitive or security reasons, say so explicitly and i’ll note it without editorializing
First, appreciate you offering the time for us to respond here – we’ll get back to you in a bit since we also want to be thoughtful on our responses here. If you have questions or are still interested in speaking afterwards, I am also happy to have a recorded+published conversation over Signal.
I am responding and addressing a couple of the points a bit sooner though since I have a request at the end of this email that is a bit time sensitive due to how it’s impacting people.
| FedRAMP authorization implies a baseline of security controls that should catch exactly this. the fix isn’t pulling the source maps, you should fix this by explaining how this passed assessment in the first place
I think this is a really fair sentiment and you are right that this is a miss regardless. To provide some additional context here, the cluster you found is one we are actively migrating to and under development. This cluster is not the same one that was evaluated for FedRAMP (which does not have the source maps visible). This new cluster is under development to provide better reliability/redundancy which was feedback from our original assessment. However, to reiterate, you are 100% right that it is never good to have unminified typescript+source maps served to the public web and it is a miss on our end.
re: onyx and the pokemon. i hear you, and i genuinely hope that’s the real story.
I understand that it’s impossible to fully trust everything I’m saying here – and if there is any reasonable way, I am happy to confirm that this is 100% the truth. Know that screenshots don’t mean much, but will still share a couple of messages from our team who I reached out to to confirm that what I sent was accurate and to provide background on the naming which ties to the above.
Furthermore, all federal contracts are public and you can confirm that we have no federal contracts today. Transparently, we are actively working on a couple of potential contracts (hence FedRAMP), but these are entirely for the purpose of employee account security and you will be able to see these engagements publicly listed if we happen to move forward.
I am writing all of this because with this context, I have one sensitive request: would you be open to swapping the folks you’ve listed to myself/the leaders/cofounders/executives of Persona rather than individual engineers? If helpful, I can provide a list of relevant people too.
I know that all of the information you’ve shared on these individuals is public and on their social profiles, and I also know that there’s no malice in your listing of them. However, the implied tie between Palantir/ICE/Persona/betrayal from your post is leading to a lot of fear/anxiety and direct/violent threats to them particularly accusing them for something that we do not do/have never been involved in (we have no relationship whatsoever with ICE, Palantir, and the other vendors listed).
Some of the folks listed are new grads/interns/people who haven’t been at Persona for a long time, and they shouldn’t have this burden placed on them. I don’t think these people are the ones that the public’s ire should be directed at, and if anyone, it should be directed at me.
I understand the intent around transparency and don’t mind if you retain the references re: Onyx/ICE/etc. I also know that this information is public and you don’t owe us anything to make this change. However, given how things have changed for folks here, I really must ask if it’s possible to not have these individuals listed.
I would really really appreciate this change and will move as quickly as possible/do whatever I can to change this!
PS – thanks for the callout re: security.txt. Will be updated shortly.
Best,
—
Celeste’s reply, Feb 17, 2026, 6:27 AM
Celeste
to me ▼hiya rick, i appreciate you reaching out
thanks for not leading with lawyers. that already puts you ahead of most companies who find their entire codebase on the front page of hacker news, so genuinely, thank you
sending the CEO instead of outside counsel says something, and i want to acknowledge that
let me go through your points.
re: the source maps. glad you’re fixing it, but i need to be clear about what we’re actually talking about. this wasn’t a misconfigured S3 bucket on some forgotten staging box. this was unminified typescript served from /vite-dev/ on a FedRAMP-authorized government endpoint, that path is vite’s development server prefix. someone deployed a dev build to production on infrastructure that already went through federal security assessment. 2,456 source files. the full dashboard codebase of a platform that processes biometric data and files reports with FinCEN. that’s kind of really bad to be honest
[It wasn’t production and it hadn’t been through security assessment and it was just Typescript]
respect for fixing it that fast btw, 2-3 hours is a pretty good response time
“we haven’t started an in-depth security review yet” is a sentence that should concern your compliance team more than my blog post does
[You need to develop the code before you can do the in depth final security review]
FedRAMP authorization implies a baseline of security controls that should catch exactly this. the fix isn’t pulling the source maps, you should fix this by explaining how this passed assessment in the first place\
re: onyx and the pokemon. i hear you, and i genuinely hope that’s the real story. unfortunately there is no way i can fully trust you here and you know this, but i’m trying to act in good faith. the blog post explicitly states we found zero references to fivecast, ICE, or immigration enforcement in all source files we found; we were careful to distinguish infrastructure correlation from code-level confirmation. that transparency is still there in the published version and it’s not going anywhere
[Celeste confirms that they found zero references to anything to do with ICE in the code]
but you have to understand that a deployment called “onyx” appearing on your government infrastructure 12 days before publication, sharing a name with ICE’s $4.2M surveillance tool, while the current administration is running the most aggressive deportation apparatus in modern history… that’s going to raise questions. a pokemon origin story is a perfectly fine answer!!!!!! but it needs to be a documented, verifiable, and quotable answer….. not something said on a call that nobody can reference later
[Celeste’s only reason for suspecting a connection with ICE is the use of the name Onyx in the code]
Re: the call, can’t do that sadly :(
not because i don’t trust you. you seem genuine and i appreciate the offer. but the 18 questions in section 0×14 aren’t the kind of thing that should disappear into a private zoom session. your platform holds biometric data for millions of people. it files SARs directly to FinCEN. it files STRs to FINTRAC tagged with intelligence program codenames. it runs PEP facial recognition with similarity scoring against your selfie. the people whose faces and passports are in your system deserve answers they can actually read.
[These are just options that can be provided by Persona in cases where a client needs them]
private conversations are where accountability goes to die. not because of malice, but because memory is fallible, quotes get disputed, and nothing is verifiable after the fact. “we talked about it on a call” isn’t transparency, even if i recorded it.
transparency is text that anyone can read, link to, and verify.
so here’s my proposal:
answer the 18 questions in writing. take your time. i’m not trying to rush you into something sloppy. be as detailed or as high-level as you’re comfortable with. if there are things you genuinely can’t answer for legal or competitive or security reasons, say so explicitly and i’ll note it without editorializing
i will publish your full response in a second part, unedited, with whatever context or corrections you want to include. no selective quoting, no editorial spin. your words, in full, next to mine :3
[Vmfunc doesn’t seem to have published the responses]
if you’d prefer something more conversational, we’re open to a recorded and published conversation on signal. the format doesn’t matter but the public record does
for what it’s worth i don’t think persona is necessarily evil. the blog post ends by acknowledging what the code doesn’t show, and we meant that. i think you built a compliance platform that does what compliance platforms do, and the harder questions are about the system that makes platforms like yours necessary in the first place. but those questions still deserve answers, and “trust us” isn’t sufficient when you’re holding people’s passports and faces… especially when you have palantir in your investors, government contracts, etc etc
the blog exists because the information was already public and nobody was asking the questions. if persona wants to answer them, that’s the best possible outcome for everyone, including persona. i’d rather publish “persona addressed every concern in detail” than “persona’s CEO asked for a private call”
this email, your original message to me, and your written responses will all be published in full. everything is on the record. i want to be transparent about that upfront so there are no surprises
email works best. i don’t check twitter DMs (they have been broken for some reason)
if that wasn’t obvious already, we’re not looking for money, or anything of the sort. we just want the people to be informed
// celeste
// vmfunc.reps: the expired security.txt on the onyx deployment (bugcrowd program, expired 2025-11-01). you might want to renew that while you’re in there.
—
Rick Song’s initial outreach email, Feb 16, 2026, 7:10 PM
Rick Song [rick@withpersona.com](mailto:rick@withpersona.com)
to celeste ▼Hi Celeste,
I’m Rick, one of the co-founders and CEO of Persona.
I came across your recent blog post (vmfunc.re) and wanted to reach out directly:
1/ Thank you for the callout re: shipping the source maps – we are looking into fixing this now! ‘withpersona-gov.com’ is currently under development and is not actively used right now. For context, we’re currently working through the FedRAMP process since there has been interest from a couple of agencies to provide identity proofing services for remote federal employees. We do not want our technology to be used by ICE or the government or for any surveillance purposes.
Unfortunately, providing the sourcemaps was an oversight by the team working on this, and we haven’t started an in-depth security review / pen test on the project yet given it’s still in early development.
2/ I’m happy to answer any/all of the 14 questions on your post about Persona and the way we operate to the best of my knowledge. For example, the Onyx name has no association with ICE (we weren’t even aware until your blog post!) – it’s actually named after a coworker’s favorite Pokemon. We do not work with any federal agency today, and this is an unfortunate name…
Happy to answer over a call live on whatever platform works best for you (Zoom, Meets, Signal, or even Discord lol). In a past life, I was an engineer and I still make mediocre contributions to our codebase semi-frequently, so I can speak at a high-level regarding our technical architecture too.
I have some time tonight if that happens to work for you? Would love to provide clarifications to some of your points sooner if possible! I’ve also reached out over Twitter to @vmfunc in case DMs are more convenient.
Best,
Rick Song
CEO | Personahttps://withpersona.com
The Rick Song / Celeste correspondence completely changes the picture.
I found it with help of Perplexity AI.
I have found several blog posts that just summarize vmfunc and show no awareness of Rick Song’s responses and often with very major mistakes about Discord too such as not aware that in their experiment they got Persona to blur out all fields except date of birth and photo and only got a pass or fail back about whether it’s adult, with all data deleted after 7 days etc.
Other major clients include Reddit and Open AI
From Reddit:
To verify your age, we partner with a trusted third-party provider (Persona) who performs the verification on either an uploaded selfie or a photo of your government ID. Reddit will not have access to the uploaded photo, and Reddit will only store your verification status along with the birthdate you provided so you won’t have to re-enter it each time you try to access restricted content. Persona promises not to retain the photo for longer than 7 days and will not have access to your Reddit data such as the subreddits you visit. Your birthdate is never visible to other users or advertisers, and is used to support safety features and age-appropriate experiences on Reddit. You can learn more about how age verification works here and about what content is restricted here.
https://www.reddit.com/r/RedditSafety/comments/1lzt65t/verifying_the_age_but_not_the_identity_of_uk/
So please don’t be scared if you come across Persona. It is a very reliable company. And it has nothing to do with ICE.
See also my
There I need to add a link back here to explain that there was a leak but a very minor inconsequential one.
CONTACT ME VIA ddebunked.org OR EMAIL
You can Direct Message me on Substack - but I check this rarely. Better, email me at support@robertinventor.com
OR contact me at our new forum
https://ddebunked.org
Please do NOT Direct Message me on Facebook any more unless you are already in contact with me.
If already in contact on FB then please understand if I don’t reply for a while except to very urgent messages
Try email or other ways to talk to me until this is sorted out.
For now I only want to talk on FB about how to message me somewhere else.
FOR MORE HELP
To find a debunk see: List of articles in my Debunking Doomsday blog to date See also my Short debunks
Scared and want a story debunked? Post to our forum which is set up for voluntary fact checking.
The forum itself is here:
Also do join our forum if you can help with fact checking or to help scared people who are panicking.
Alternatively you can post to our Facebook group. Please look over the group rules before posting or commenting as they help the group to run smoothly
Facebook group Doomsday Debunked
However I am not able to comment or post there at present because
SEARCH LIST OF DEBUNKS
You can search by title and there’s also an option to search the content of the blog using a google search. Try different terms e.g. Russia, Putin etc as it only searches the title.
CLICK HERE TO SEARCH: List of articles in my Debunking Doomsday blog to date
NEW SHORT DEBUNKS
I do many more fact checks and debunks on our Facebook group than I could ever write up as blog posts. They are shorter and less polished but there is a good chance you may find a short debunk for some recent concern.
I often write them up as “short debunks”
See Latest short debunks for new short debunks
I also tweet the debunks and short debunks to my Blue Sky page here:
I do the short debunks more often but they are less polished - they are copies of my longer replies to scared people in the Facebook group.
I go through phases when I do lots of short debunks. Recently, I’ve taken to converting comments in the group into posts in the group that resemble short debunks and most of those haven’t yet been copied over to the wiki.
TIPS FOR DEALING WITH DOOMSDAY FEARS
If suicidal or helping someone suicidal see my:
BLOG: Supporting someone who is suicidal
If you have got scared by any of this, health professionals can help. Many of those affected do get help and find it makes a big difference.
They can’t do fact-checking, don’t expect that of them. But they can do a huge amount to help with the panic, anxiety, maladaptive responses to fear and so on.
Also do remember that therapy is not like physical medicine. The only way a therapist can diagnose or indeed treat you is by talking to you and listening to you. If this dialogue isn’t working for whatever reason, do remember you can always ask to change to another therapist and it doesn’t reflect badly on your current therapist to do this.
Also check out my Seven tips for dealing with doomsday fears based on things that help those scared, including a section about ways that health professionals can help you.
I know that sadly many of the people we help can’t access therapy for one reason or another - usually long waiting lists or the costs.
There is much you can do to help yourself. As well as those seven tips, see my:
BLOG: Breathe in and out slowly and deeply and other ways to calm a panic attack
BLOG: Tips from CBT
— might help some of you to deal with doomsday anxieties
PLEASE DON’T COMMENT HERE WITH POTENTIALLY SCARY QUESTIONS ABOUT OTHER TOPICS - INSTEAD JOIN OUR NEW FORUM ddebunked.org
PLEASE DON’T COMMENT ON THIS POST WITH POTENTIALLY SCARY QUESTIONS ABOUT ANY OTHER TOPIC:
INSTEAD PLEASE COMMENT IN OUR NEW FORUM HERE:
It’s just a forum not social media. No age verification. Set up by myself with free open source software Flarum.
For details:
If you have any issues joining it do let me know.
Why I ask you to post to our forum with anything scary off topic instead of here
The reason I ask you to post there instead of comment with your concerns about unrelated topics here is that I often can’t respond to comments here for some time. The unanswered comment can scare people who come to this post for help on something else
Also even an answered comment may scare them because they see the comment before my reply.
Do comment here with anything that is on topic for this post, E.g. if you spot any mistakes however small please let me know.
Also, though your first comment should be on topic, it is absolutely fine to digress and go off topic in conversations here in a natural way if that is how the conversation develops.
This is specifically about off topic comments here hat might scare people on a different topic.
PLEASE DON’T TELL A SCARED PERSON THAT THE THING THEY ARE SCARED OF IS TRUE WITHOUT A VERY RELIABLE SOURCE OR IF YOU ARE A VERY RELIABLE SOURCE YOURSELF - AND RESPOND WITH CARE
This is not like a typical post on substack. It is specifically to help people who are very scared with voluntary fact checking. Please no politically motivated exaggerations here. And please be careful, be aware of the context.
We have a rule in the Facebook group and it is the same here.
If you are scared and need help it is absolutely fine to comment about anything to do with the topic of the post that scares you.
But if you are not scared or don’t want help with my voluntary fact checking please don’t comment with any scary material.
If you respond to scared people here please be careful with your sources. Don’t tell them that something they are scared of is true without excellent reliable sources, or if you are a reliable source yourself.
It also matters a lot exactly HOW you respond. E.g. if someone is in an area with a potential for earthquakes there’s a big difference between a reply that talks about the largest earthquake that’s possible there even when based on reliable sources, and says nothing about how to protect themselves and the same reply with a summary and link to measures to take to protect yourself in an earthquake.








PLEASE DON’T COMMENT ON THIS POST WITH POTENTIALLY SCARY QUESTIONS ABOUT ANY OTHER TOPIC
Also please check the purpose of this substack - to help people scared of many things. Welcome:
- questions if you are still scared and need help
- fact checks if I got anything wrong however small
- help with debunking
Please don't post potentially scary things here unless you are yourself scared and needing help.
FOR POTENTIAL SCARY QUESTIONS ABOUT OTHER TOPICS YOU WANT DEBUNKED - PLEASE COMMENT IN OUR NEW FORUM HERE
https://ddebunked.org
There are many there who can answer you not just me. And it is setup for voluntary fact checking and far easier to use than comments here
https://ddebunked.org
It’s just a forum not social media. No age verification. Set up by myself with free open source software Flarum.
For details see my:
https://robertinventor.substack.com/p/our-own-new-discussion-forum-for
We only need your user name and email address to join and the email address is just for notifications, we don't look at it (unless needed to help you or for debugging) or share with anyone.
If you have any issues joining it do let me know.